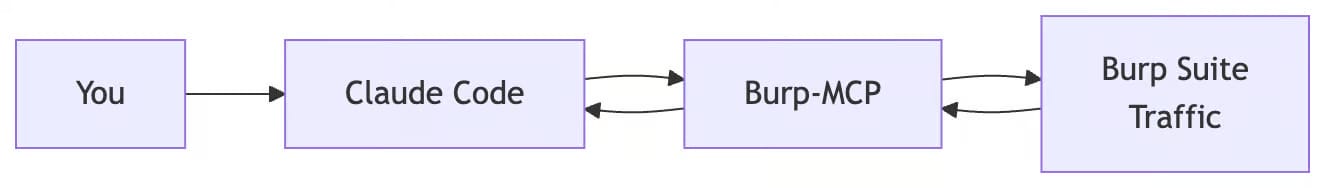
Claude Code x Burp-MCP flow
IDOR hunting involves repetitive manual testing. You scroll through hundreds of Burp history entries, spot a parameter that looks promising, send it to Repeater, swap in another user's ID, check the response. Then do it again. And again.
Claude Code with Burp MCP changes that. You describe what you want to test, and it handles the repetitive work.
Why AI for IDOR Testing
IDOR happens when an app exposes internal objects (files, records, user data) through identifiers without checking if you're allowed to access them. The classic example: changing /api/users/123/profile to /api/users/456/profile and seeing someone else's data.
Manual vs AI-Assisted:
Task | Manual Steps | AI-Assisted |
|---|---|---|
Filter endpoints from proxy history | 5-10 steps | 1 prompt |
Identify IDOR-vulnerable parameters | 10-15 steps | 1 prompt |
Test cross-user access | 20+ steps | 1 prompt |
Generate findings report | 5-10 steps | 1 prompt |
~40 manual steps → 4 prompts
Setup
Step 1: Install IDOR Testing Skill
npx skills add https://github.com/sickn33/antigravity-awesome-skills --skill 'idor-testing'Step 2: Configure Burp MCP
If you haven't set up Burp MCP yet, see the previous post:
Step 3: Create CLAUDE.md Configuration
Create a file name
CLAUDE.mdand paste below content
# Pentest Project
## Target Scope
- *.example.com
- api.example.com:443
## Application Context
- **Target:** E-commerce API for ACME Corp
- **Auth Flow:** JWT-based authentication, refresh tokens expire in 7 days
- **User Roles:** User, Admin
- **Business Logic:** Cart -> Checkout -> Payment (Stripe integration)
- **Stack:** Python/FastAPI backend, PostgreSQL, Redis cache
- **Known Issues:** Legacy endpoints at /api/v1/ still active
## Tools Available
- Burp Suite Professional
- burp-mcp extension loaded
## Claude Skills
- IDOR Testing
## Output
- Save reports to ./reports/
- Use markdown formatReplace the target scope and application context with your actual engagement details.
Use Case: IDOR Testing Demo
Phase 0: Inputs & Prerequisites
Before you start, you need a few things:
Prerequisite | Description | Example |
|---|---|---|
Multiple User Accounts | At least two test accounts to verify cross-user access | user1, user-target |
Application Flow Knowledge | Understanding of how objects are referenced | IDs, filenames, UUIDs in API calls |
Information to Prepare:
Test Account Credentials
Username and auth tokens/cookies for each account
Minimum: 2 accounts (attacker and victim)
Better: 3+ accounts covering different roles
Resource Identifiers
Known object IDs belonging to each test account
Example: user1's order_id = 67890, user-target's order_id = 12345
Phase 1: Filter API Endpoints for IDOR
First, identify parameterized HTTP requests that may contain IDOR vulnerabilities.
Prompt:
Send below prompt to Claude Code
Identify **parameterized HTTP requests** from Burp MCP history that may be vulnerable to **IDOR**
Tasks:
* Extract requests with parameters in **path, query, or body**
* Focus on identifiers like `id`, `user_id`, `account_id`, `order_id`, `transaction_id`, `uuid`, numeric IDs, or username
* Prioritize requests that **retrieve, update, or delete user-related resources**What this does:
Queries the Burp proxy history through MCP and filters for requests containing object identifiers that could be manipulated.
Why this matters:
Manually reviewing hundreds of proxy history entries is time-consuming and error-prone. This prompt instantly surfaces the most likely IDOR targets, letting you focus testing effort where it counts.

Claude code filter the API Endpoint applicable for IDOR Testing
Phase 2: IDOR Testing on Filtered Endpoints
Now test those endpoints for authorization bypasses.
Prompt:
Send below prompt to Claude Code
Find IDOR vulnerabilities on the previously identified parameterized API endpoints
Use the following test accounts to validate **cross-user access**:
**Primary User (Attacker)**
* Username: user1
* Cookie: auth=eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VySWQiOiI2OWIzMDIyOTU0Y2I4ZjljNDkzN2NhY2MiLCJ1c2VybmFtZSI6InVzZXIxIiwiaXNBZG1pbiI6ImZhbHNlIiwiaWF0IjoxNzczMzM5MTg1fQ.vYSpSdAt-5NyZZXh9Q3KXAupWmOnOoci-oDbt8VfbFk
**Target User (Victim)**
* Username: user-target
* Cookie: auth=eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VySWQiOiI2OWIzMDJkMDU0Y2I4ZjljNDkzN2NiMTMiLCJ1c2VybmFtZSI6InVzZXItdGFyZ2V0IiwiaXNBZG1pbiI6ImZhbHNlIiwiaWF0IjoxNzczMzM5MzQ4fQ.OgVjE8T6ByH1AeTPLw9x58n9gPd-4_GeJuN8xTAbtHU
Task:
* Send requests using the **Primary User session** while modifying object identifiers to reference resources belonging to the **Target User**
* Identify any endpoints where **unauthorized access, modification, or deletion of another user's resources is possible**
What this does:
Uses the Primary User's session to send requests
Replaces identifiers with Target User's resource IDs
Compares responses to detect unauthorized access
Flags endpoints where authorization checks are missing
Real output from actual session:
Testing endpoint: GET /api/getNote?username=user-target
- Request with Primary user (user1) cookie + Target username
- Response: 200 OK with {"status":"success","note":"user-target notes"}
[VULNERABLE] IDOR detected on GET /api/getNote?username=
- Primary user (user1) can access user-target's notes
- No authorization check - accepts any username parameter
- Severity: Critical
Testing endpoint: GET /api/getNote?username=admin
- Request with Primary user (user1) cookie + admin username
- Response: 200 OK
Testing endpoint: POST /api/getNote (with username in body)
- Request with Primary user cookie + Target username in body
- Response: 200 OK with {"status":"success","note":"IDOR write test!"}
[VULNERABLE] IDOR WRITE detected on POST /api/getNote
- Primary user can modify any user's notes
- Severity: CriticalWhy this matters:
This replaces manual request tampering in Burp Repeater for each endpoint. Claude Code handles the repetitive work of swapping identifiers, resending requests, and comparing responses, tasks that would take hours manually.

Claude Code found IDOR bug

Claude Code found IDOR bug
Phase 3: Manual Validation with Burp Repeater
For each finding, create a Burp Repeater tab for manual confirmation.
Prompt:
Send below prompt to Claude Code
Create Burp Repeater tabs via burp-mcp for ALL attack payloads (including failed ones) for manual verificationThis sends the malicious request to Burp Repeater where you can:
Modify parameters manually
Test additional variations
Document the exploit for your report
Create proof-of-concept screenshots
Why this matters:
Automated findings need manual confirmation before reporting. This step bridges AI-assisted discovery with human verification, ensuring findings are valid and reproducible.

Claude Code created Repeater tab
Summary of Findings
Prompt:
Send below prompt to Claude Code
Generate a summary report of all IDOR vulnerabilities found during testing
Include:
* Vulnerable endpoint and HTTP method
* Parameter that can be manipulated
* Description of unauthorized access possible
* Severity rating (Critical, High, Medium, Low)
* Proof of concept steps
* Remediation recommendations
Save the report to ./reports/idor-findings.mdActual findings from session:
Endpoint | Method | Parameter | Vulnerability | Severity |
|---|---|---|---|---|
/api/getNote?username= | GET | username | View any user's notes (including admin) | Critical |
/api/getNote | POST | username (body) | Modify any user's notes | Critical |
/api/allUsers | GET | - | Enumerate all registered users | Medium |
Why this matters:
Good documentation saves time later. The generated report is a starting point you can adapt for client deliverables or bug bounty submissions
What to Improve
Tips for Better Results:
Provide complete application context in CLAUDE.md
Include all user roles (User, Admin, Manager)
Test both horizontal (same role) and vertical (different roles) privilege escalation
Add authentication headers/cookies for all test accounts
Review business logic to understand resource ownership
Conclusion
AI-assisted IDOR testing with Claude Code and Burp MCP decreases the time spent on repetitive authorization testing. Instead of manually testing each endpoint, you can:
Filter hundreds of requests automatically
Test cross-user access across multiple accounts
Document findings in a consistent format
Focus manual effort on validation and exploit development
This approach works for bug bounty hunting, penetration testing engagements, and API security assessments where time is limited and attack surfaces are large.
Further Reading
Subscribe to Secengai.com for more tutorials on applied AI for security engineering.
