TL;DR: Build a custom Claude Code command to automate phishing email analysis with Claude's header inspection, URL/attachment extraction, and threat intelligence enrichment,all executed in a sandboxed environment. Analysis time: 20 minutes → 8 seconds.
What is Email Phishing Analysis (and Why It's Still Manual)
Security teams spend 15-30 minutes per phishing email performing repetitive tasks:
Parse email headers to identify spoofed senders
Extract all URLs and check domain reputation
Calculate file hashes for attachments
Query VirusTotal and threat intelligence feeds
Document findings in incident tickets
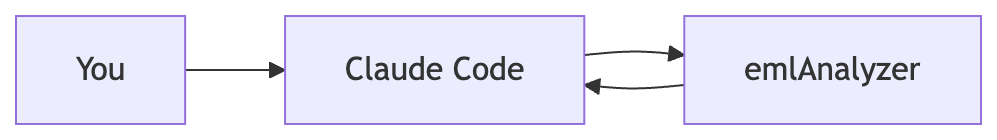
Current tools parse email structure but require manual interpretation,analysts copy-paste indicators into VirusTotal, cross-reference domains, and write reports manually. This tutorial uses Claude Code's AI reasoning with eml_analyzer.
⏳ Result: Time saving = analysis time from 20+ minutes to 8 seconds
What is an .EML File
An .eml file stores email messages in RFC 822 format,a plain text structure containing:
From: "PayPal Support" <[email protected]>
To: [email protected]
Subject: Urgent: Verify Your Account
Date: Mon, 23 Mar 2026 14:32:01 +0000
MIME-Version: 1.0
Content-Type: multipart/mixed; boundary="----=_Part_12345"
------=_Part_12345
Content-Type: text/html; charset="UTF-8"
<html>
<body>Click here to verify: <a href="http://paypal-verify.ml">Verify Now</a></body>
</html>
------=_Part_12345
Content-Type: application/pdf; name="invoice.pdf"
Content-Transfer-Encoding: base64
JVBERi0xLjQKJeLjz9MKMyAwIG9iago8PC9MZW5ndGggMTQ...
------=_Part_12345--Key components:
Section | Purpose | Forensic Value |
|---|---|---|
Headers | Metadata (From, To, routing) | Identify spoofing, trace sender IP |
Body | Message content (HTML/plain text) | Detect social engineering language |
Attachments | Files encoded in MIME format | Hash analysis, malware detection |
Email clients (Outlook, Gmail, Thunderbird) export to .eml format, preserving complete forensic evidence including headers, routing data, and authentication results.
Why AI + Claude Code Makes Email Analysis Better
Traditional analysis means switching between VirusTotal, regex scripts, and ticket systems. Claude Code runs all three in one command:
Pattern recognition:
Detects display name spoofing and domain mismatches
Identifies social engineering language patterns
Recognizes URL obfuscation and suspicious TLDs
Automation with context:
Extracts all indicators without regex scripting
Cross-references domains against known campaigns
Generates structured reports automatically
Setup
Step 1: Install eml_analyzer
Install the Python-based EML parsing tool:
pip install eml-analyzerStep 2: Create the Command Directory
Claude Code loads custom commands from ~/.claude/commands:
mkdir -p ~/.claude/commandsStep 3: Create the Command Definition
Create ~/.claude/commands/phishing-analysis.md:
---
description: Analyze .eml file for phishing
---
You are an email security analyst. Your job: given a provided **.eml** file, decide if it's **phishing**, **suspicious**, **benign**, or **unknown**, and explain why.
## Analysis Command Sequence
1. `emlAnalyzer -i $ARGUMENTS --header --url --attachments --text --html --structure --format json`
2. Parse and structure the JSON output for systematic analysis
3. Apply scoring methodology systematically
4. Generate final verdict and recommendations
## What to extract
1) **Header auth & routing**
- From/Reply-To/Return-Path, Envelope-From
- Authentication-Results (SPF/DKIM/DMARC pass/fail/none)
- Display-name spoofing; lookalike domains (homoglyphs, extra chars, wrong TLD)
2) **Body content**
- Urgency/threats (account lock, payroll, crypto withdrawal, invoice, OTP reset)
- Requests for credentials, MFA codes, payments, gift cards, crypto
- Brand impersonation; mismatched branding vs domain
3) **Links & artifacts**
- Flag mismatched link text vs href; shorteners; IP URLs; punycode; suspicious TLDs
- Attachments (.html, .zip, .js, .lnk, .iso, .xlsm, etc.)
## Scoring (heuristic; additive, then clamp 0–100)
- High-risk (+25 each): auth fail (SPF/DKIM/DMARC), credential/payment request, risky attachment
- Medium (+10 each): first-contact + urgent tone, Reply-To ≠ From
- Low (+5 each): minor grammar, generic greeting
- Map score → verdict: ≥60: phishing | 40–59: suspicious | 20–39: benign (low confidence) | <20: benign
## Output (Markdown format)
### Executive Summary
- **Verdict**: Phishing | Suspicious | Benign | Unknown
- **Confidence**: 0-100
- **Risk Level**: Critical | High | Medium | Low
- **Key Findings**: Top 3 most concerning indicators
### Authentication Results
- SPF/DKIM/DMARC: pass|fail|none|missing
### Sender Analysis
- Display-name spoof, domain lookalike detection
### Links, Attachments, Content Indicators
- Extracted URLs with flags (ip, shortener, punycode, suspicious_tld)
- Risky attachments with reasoning
### Recommended Actions
- Security actions (e.g., "Report to security," "Do not click links")
Command should appeared on Claude Code interactive mode
Demo: Email Phishing Analysis
Step 1: Download Sample Phishing Email
curl -o sample-3864.eml https://raw.githubusercontent.com/rf-peixoto/phishing_pot/refs/heads/main/email/sample-3864.emlStep 2: Enable Sandbox Mode
Sandbox isolation stops malicious attachments from writing files outside the project directory or making network calls to unlisted domains.
Prompt: Send below prompt to Claude Code
/sandbox
Sandbox settings
Why sandbox matters: The sandbox blocks file writes outside your project directory and network calls to domains not on your allowlist.
Step 3: Run the Analysis
Prompt: Send below prompt to Claude Code
/phishing-analysis @sample-3864.eml
Running /phishing-analysis
Understanding the Analysis Output
Claude processes the sample-3864.eml file and returns:

Finding from email analysis
Follow-up Prompts
After the initial analysis, use these prompts to investigate further:
Prompt: Send below prompt to Claude Code
Analyze the sending IP and domain reputation. Check if ali001.sarakzit.za.com has been reported in abuse databases.Prompt: Send below prompt to Claude Code
Expand all shortened URLs and analyze the final destinations. Check URLhaus and VirusTotal for these domains.Prompt: Send below prompt to Claude Code
Search for similar phishing emails using the same tracking infrastructure (199.192.27.195). Are there related campaigns?Prompt: Send below prompt to Claude Code
If attachments are present, calculate file hashes and check against malware databases. Analyze PDF/Office documents for embedded scripts.Prompt: Send below prompt to Claude Code
Show the email routing path and timing. Identify any unusual delays or routing through suspicious countries.Further Improvements
Threat Intelligence Integration: Enable automated IoC enrichment by integrating VirusTotal MCP for URL/hash reputation, URLhaus MCP for malicious URL databases, and AbuseIPDB MCP for sender IP scoring. See Further Reading for MCP server links.
Convert to Reusable Skill: Move command to
~/.claude/skills/directory with parameters (--threat-intel flag, output format options) for team sharing and version control. Skills enable programmatic invocation and workflow automation.
Security Considerations
Analyzing malicious emails is risky. Sandbox isolation provides defense-in-depth protection.
Why Sandbox is Critical
Threat scenarios:
Malicious attachments: PDF with embedded JavaScript, Office macros with payload
Network callbacks: Tracking pixels, web bugs connecting to attacker infrastructure
Filesystem access: Malware attempting to write to startup folders or system directories
Sandbox protections:
Risk | Mitigation |
|---|---|
Attachment execution | Filesystem isolation prevents write outside project directory |
Network exfiltration | Network allowlist blocks unauthorized domains |
System modification | OS-level enforcement (Seatbelt/bubblewrap) restricts syscalls |
Alternative Sandbox
Conclusion
This tutorial demonstrates how Claude Code performs automated phishing email analysis by combining eml_analyzer parsing with AI pattern recognition, reducing analysis time from 20+ minutes to 8 seconds. The sandboxed workflow safely extracts IoCs, detects spoofing and social engineering tactics, and generates actionable security reports without manual intervention. Integrate threat intelligence MCPs (VirusTotal, URLhaus, AbuseIPDB) to further enhance detection capabilities and scale from individual investigations to enterprise-wide incident response automation.
Further Reading
Related Tools:
eml_analyzer - Python library for parsing EML files
PhishTool - Community phishing analysis platform
URLhaus - Malware URL database
AbuseIPDB - IP address abuse reporting database
Ready to apply AI to phishing analysis?
Subscribe to Secengai Newsletter for weekly actionable content on AI for security engineers.

